Why you should prioritize security and privacy
In an era where data fuels business operations, ensuring robust data security and privacy measures is paramount. At IDS Consulting, we recognize the critical importance of safeguarding sensitive information from unauthorized access and breaches. Let’s delve into strategies that organizations can employ to fortify their data defenses.
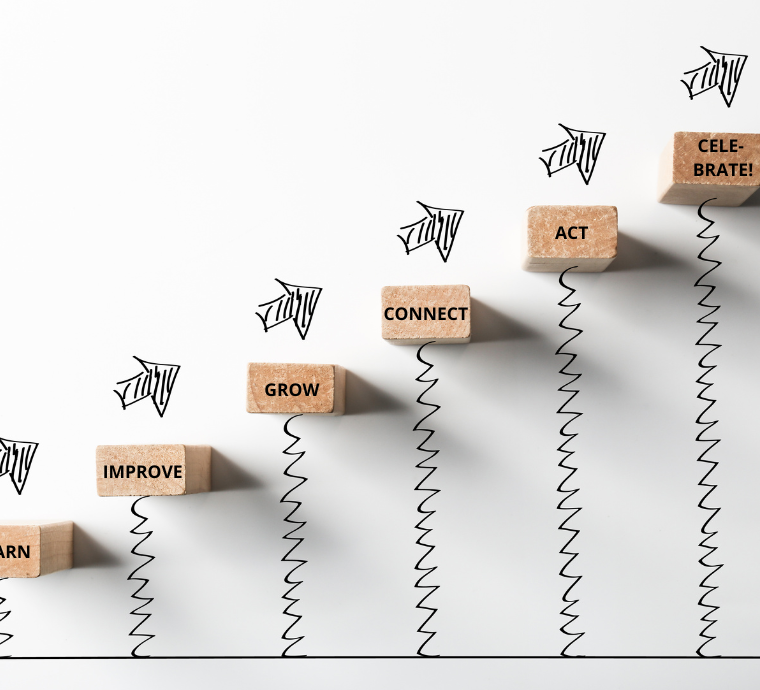
10 Steps for better Data Security and Privacy
1. Implement Robust Authentication: Strengthen access controls through multi-factor authentication (MFA). This adds an extra layer of security, requiring users to verify their identity through multiple methods.
2. Encrypt Sensitive Data: Employ encryption algorithms to encode sensitive information both in transit and at rest. This ensures that even if unauthorized access occurs, the intercepted data remains indecipherable.
3. Regular Security Audits: Conduct routine security audits and assessments to identify vulnerabilities. This proactive approach allows organizations to patch potential weak points before they can be exploited.
4. Employee Training and Awareness: Human error is a common factor in data breaches. Educate and train employees on security best practices and the potential risks associated with their roles.
5. Data Backup and Recovery: Establish robust data backup procedures to prevent data loss in case of a breach. Implement a comprehensive recovery plan to minimize downtime and ensure business continuity.
6. Update and Patch Systems: Regularly update and patch software, operating systems, and applications. Outdated systems are more susceptible to vulnerabilities that can be exploited by malicious actors.
7. Monitor User Activities: Implement real-time monitoring of user activities to detect anomalies. Unusual patterns of access or data retrieval can indicate a potential security threat.
8. Privacy by Design: Incorporate privacy measures from the outset of any data-related project. Privacy should be an integral part of the system architecture rather than a retrofitted feature.
9. Compliance with Data Protection Regulations: Stay abreast of data protection regulations relevant to your industry. Compliance not only avoids legal repercussions but also ensures a comprehensive approach to data security and privacy.
10. Secure Third-Party Integrations: If using third-party services, thoroughly vet their security measures. Ensure that their integration into your systems doesn’t introduce vulnerabilities.

Conclusion
At IDS Consulting, we stand as your ally in fortifying data security and privacy. Our expertise ensures that your data remains shielded against the ever-evolving landscape of cyber threats.
Overwhelmed? Don’t worry, it’s our job to take care of all of these details. You just set the context and objectives, and we will take it from there. Let’s have a chat and detail your context.